This is the best summary I could come up with:
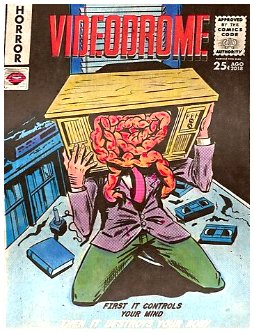
Days after it was knocked offline by a sweeping, years-in-the-making law enforcement operation, the notorious Russia-based LockBit ransomware group has returned to the dark web with a new leak site complete with a number of new victims.
Law enforcement claiming overwhelming victory while the apparent LockBit ringleader remains at large, threatening retaliation, and targeting new victims puts the two at odds — for now.
While the NCA promised a big reveal of the gang’s long-standing leader, who goes by the name of “LockBitSupp,” the agency disclosed little about the administrator in a post to LockBit’s own compromised dark web leak site on Friday.
U.S. law enforcement agencies have also offered a multi-million dollar reward for details “leading to the identification or location of any individual(s) who hold a key leadership position” in the LockBit gang — suggesting the authorities either don’t have that information or cannot yet prove it.
Take another Russia-based ransomware gang: ALPHV, also known as BlackCat, last year was dealt a similar blow when law enforcement agencies seized its dark web leak site and released decryption keys so victims could regain access to stolen files.
Just days later, the ALPHV announced it “unseized” its leak site and claimed the FBI only had decryption keys for 400 or so companies — leaving more than 3,000 victims whose data remains encrypted.
The original article contains 830 words, the summary contains 222 words. Saved 73%. I’m a bot and I’m open source!